
When the word “cybersecurity” is mentioned, the popular show Mr. Robot immediately comes to mind. The main character – Elliot, played by Rami Malek, is constantly on the warpath. He works as a cybersecurity engineer for a billion-dollar corporation by day and moonlights as a mythical sort of Batman hacker at night.
Mr. Robot quite well portrays what working in cybersecurity entails, although a little more glamorous. As the internet domains grow, more web resources are deployed, and the internet becomes a hot commodity with frequent malware and ransomware attacks, cybersecurity has become more important than ever to counter these threats. These threats are related to personal information, financial assets, and even national security.
A cybersecurity path is exciting and incredibly relevant for students considering their future career prospects. Within this quick read, we will explore three rewarding career options within cybersecurity, i.e., Network Engineer, Cybersecurity Analyst, and Ethical Hacker. Plus, in case you are faced with a “Who will do my essay on cybersecurity?” scenario, this article is right up your alley.
Let’s jump right into it!
Cybersecurity Essentials
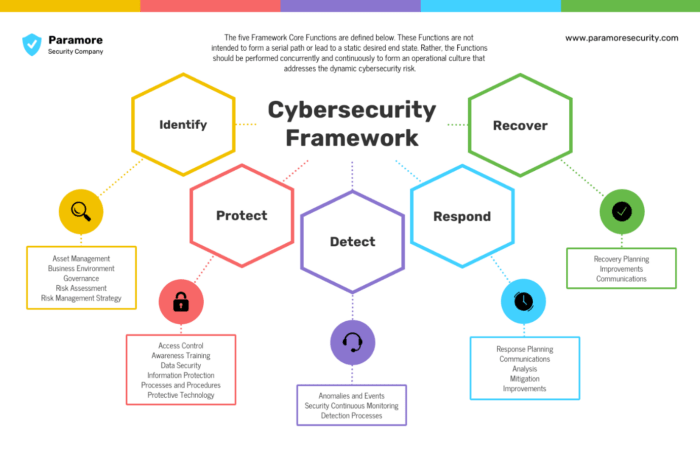
Before we explore these three career options, let’s get a brief overview of what a cybersecurity career entails. These are essentially defined in the Five Framework network diagram shown below. To get an overview of cybersecurity, think about the protection of computer systems, networks, and data from unauthorized access, cyberattacks, and data breaches. Cybersec overall needs one to have a strong foundation in math, computer science, and information technology.
Also, you’ll need a grip on networking, and knowledge of cloud security and operating systems is also required to kickstart your career in cybersecurity. Cybersecurity jobs can range from entry-level to executive management, depending on certifications and relevant experience. Now, let’s get into these three cybersecurity career paths that are both lucrative and intellectually fulfilling.
Network Engineer
When you hear about a security breach in the world’s Top 500 companies, network engineers will most likely come to mind first. Network engineers plan, install, and maintain the networks that enable data transmission within businesses. Typically, these folks are responsible for installing, maintaining, and supporting network gear and software, including switches, routers, and firewalls.
Network engineers play a vital part in ensuring data moves easily, safely, and effectively. These engineers typically work in various industries, including technology giants like FAANG (Facebook, Apple, Amazon, Netflix, and Google) companies, where they manage complex and expansive networks.
Typical Roles and Responsibilities
The typical role of a network engineer includes:
Network Infrastructure Design: Network engineers plan and design network architectures, including the layout of routers, switches, and other networking hardware. Factors like scalability and security are usually at the top of their design agenda.
Network Configuration and Maintenance: Network engineers configure and maintain the hardware and software components once a network is designed. The network needs to be optimized for performance while remaining reliable even during uptimes.
Security Implementation: Network engineers often implement security measures such as firewalls, intrusion detection systems (IDS), and virtual private networks (VPNs) to protect enterprise systems.
Troubleshooting and Problem Resolution: One of the key responsibilities of network engineers is to troubleshoot and find solutions quickly while reducing downtimes.
Performance Optimization: Network engineers continually monitor network performance, looking for ways to optimize data flow while reducing system latency during uptimes.
Network engineers are well-remunerated, according to Indeed.com. The average annual salary for a network engineer in the US is $94,510, while executives and those most experienced earn upwards of $150,000.
Cybersecurity Analyst
Cybersecurity analysts are usually the first line of defense against cyberattacks, their core function being the protection of sensitive data. They oversee tracking networks and systems for security lapses, studying security information, and handling incidents.
Cybersecurity analysts play a critical role in spotting weaknesses and guaranteeing the overall safety of a company’s digital assets. In order to guarantee that the company’s data processing procedures are compliant, they also monitor policies.
Typical Roles and Responsibilities
Threat Detection and Monitoring: Cybersecurity analysts use specialized tools and techniques to monitor network traffic and identify suspicious activities. They analyze security data to detect potential threats.
Incident Response: Cybersecurity analysts lead the response efforts when a security incident occurs. This may involve isolating affected systems, mitigating the impact, and conducting forensic analysis to understand the breach.
Vulnerability Assessment: They conduct regular vulnerability assessments to identify weaknesses in systems and applications, then recommend and implement security patches and configurations.
Security Policy Development: Cybersecurity analysts help develop and enforce security policies and procedures to maintain a secure environment.
User Awareness Training: They often educate employees about cybersecurity best practices to reduce the risk of human error.
According to Glassdoor, the average salary for a Cybersecurity analyst in the US is $97,119, with top earners in FAANG companies earning as much as $190,576.
Ethical Hacking
A hacker is usually considered someone who gains unwanted entry into a computer system or network. However, contrary to common misconception, hacking doesn’t always need to be done with malicious intent.
Ethical hacking is also often referred to as penetration testing or white-hat hacking. Ethical hackers are cybersecurity professionals who voluntarily step into the shoes of malicious hackers, with the key difference being their intent to fortify rather than exploit. Let’s explore the White Hat profession a bit further.
What Does an Ethical Hacker Do?
A security expert known as a penetration tester, also known as an ethical hacker, initiates simulated assaults against a client’s network or systems to look for vulnerabilities and weaknesses. They want to show potential weak spots in the target network and how a malicious attacker can exploit them so their clients can plug any holes before a genuine attack happens.
Some of their typical roles and responsibilities include:
Penetration Testing: Ethical hackers conduct penetration tests on systems, applications, and networks to simulate cyberattacks. This involves the use of various tools and techniques to uncover vulnerabilities.
Security Assessment: They assess the overall security posture of an organization, identifying areas that need improvement and recommending security measures.
Security Research: Ethical hackers stay up-to-date with the latest threats and hacking techniques, ensuring they are well-prepared to defend against emerging risks.
Report Generation: Ethical hackers provide detailed reports to the organization after conducting tests, outlining vulnerabilities, and suggesting remediation steps.
Security Training: They may also provide training and awareness programs to educate employees about cybersecurity best practices.
So, what does the White Hat arsenal look like?
- Kali Linux: This is the default OS for pen-testing systems. While you can get Kali Linux running on its own hardware, most ethical hackers usually run Kali Linux on a virtual machine that simulates this environment. Kali is run by Offensive Security (OffSec).
- Nmap: As an ethical hacker, you’ll be curious about everything that runs through ports, including which ports are open and what’s running through those ports. Nmap, short for Network Mapper, is the go-to tool for this recon operation.
- Wireshark: This network protocol analyzer allows you to understand the enabling traffic passing through your network and is the best framework to drill through regular TCP/IP issues.
- Metasploit: This has been aptly dubbed as the most widely used penetration testing framework and comes pre-installed on Kali Linux. It offers a command line interface for regular users, although users can pay for an additional GUI license.
Besides these tools, ethical hackers should ideally be proficient in programming languages such as Python and scripting languages for crafting custom exploits. Besides, the knowledge of different OSs, such as Windows, Linux, and macOS, comes in handy.
Cybersecurity Certifications
Certifications like Certified Ethical Hacker (CEH) and Offensive Security Certified Professional (OSCP) validate the expertise of ethical hackers. The CEH leverages a wide array of skillset training, ranging from Honeypots, Cryptography, SQL injection, Sniffers, and Denial of Service attacks.
Additionally, CompTIA Security+ provides a great base certification for entry-level positions in the industry. Ethical hackers are perpetual students of the cybersecurity world, continuously adapting to evolving threats and technologies.
Starting Your Journey Right Out of High School
There are a few things to think about for kids who want to start working in cybersecurity right out of high school or college kids with no cybersecurity background. While a bachelor’s degree is useful in the field of teaching, it is not necessarily required. For education, while a bachelor’s degree is valuable, it’s not always mandatory. You can explore associate degree programs, technical certificates, or online courses in cybersecurity to gain foundational knowledge.
Additionally, earning relevant certifications can bolster your cybersecurity credentials. Start with entry-level certifications like CompTIA Network+ or CompTIA Security+ and progress to more advanced ones as you gain experience.
Hands-on Experience is a must in the cybersecurity world. Participate in internships, work on personal projects, or contribute to open-source cybersecurity initiatives. Real-world experience is highly regarded in this field.
Finally, networking gives you a great place to land in case one gig doesn’t work out. Attend cybersecurity conferences and seminars, and join professional organizations such as (ISC)² or ISACA. Networking can open doors to job opportunities and mentorship.
Wrapping Up
A career in cybersecurity offers endless opportunities for growth and impact in an increasingly digital world. Whether you choose to become a Network Engineer, Cybersecurity Analyst, or Ethical Hacker, the common thread is a commitment to safeguarding digital assets and data.
You can embark on a fulfilling journey in this dynamic and essential field by building a strong educational foundation, acquiring relevant skills, and continuously learning. So, are you ready to protect the digital frontier? Your cybersecurity adventure begins here.

